


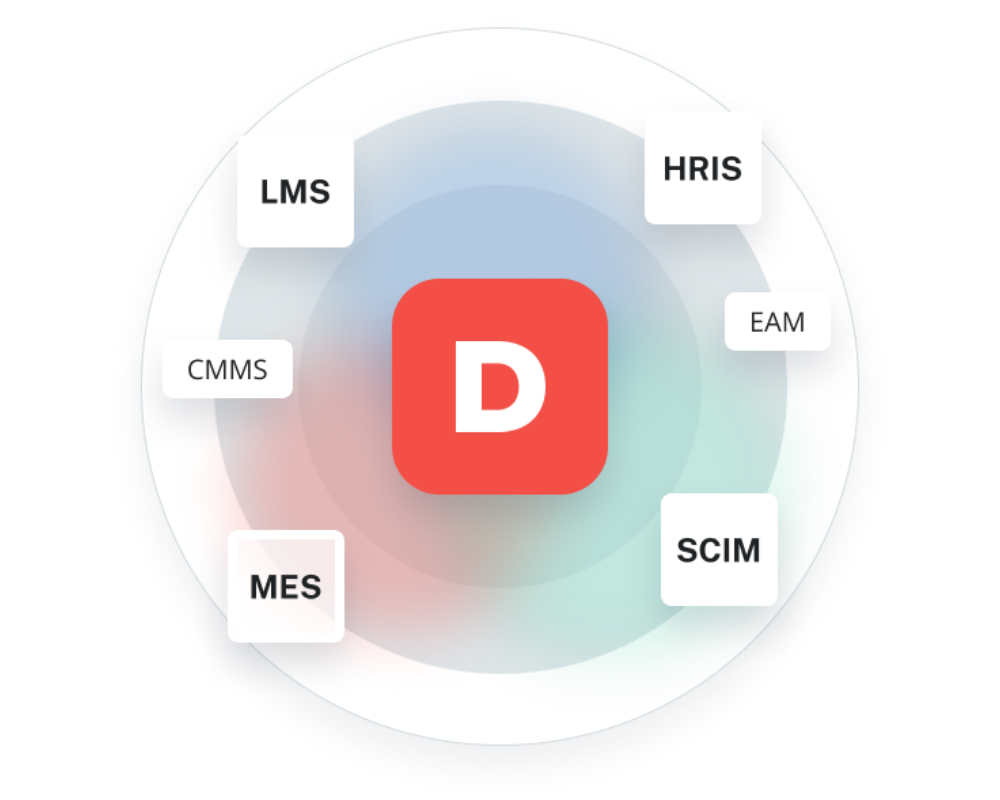
Connect Dozuki with your essential business systems to pass information, scale operations, and increase efficiency. Save time switching between applications and push OEE data from Dozuki into your LMS, QMS, ERP, or any other system with API/Webhook capabilities.

Our team of experts provides assistance across time zones to enable full adoption and troubleshooting.

Our core infrastructure is spread across multiple availability zones to keep your site running without interruption.

Dozuki is built with customer data protection and security as our top priority. Our teams work within a modern technology stack that aligns with our strict information security program and incorporates best practices throughout development.